Hackers have Watch Flesh Clerk Who Shoves You Up And Down Onlinediscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 Wordle today: The answer and hints for January 28, 2025
Wordle today: The answer and hints for January 28, 2025
 Treacherous Passage
Treacherous Passage
 Twitch updates: Vertical video and dual streaming
Twitch updates: Vertical video and dual streaming
 Staff Picks: Cycling, Skiing, and an Island of Solitude by The Paris Review
Staff Picks: Cycling, Skiing, and an Island of Solitude by The Paris Review
 Trump praises storm response as historic disaster unfolds in Houston
Trump praises storm response as historic disaster unfolds in Houston
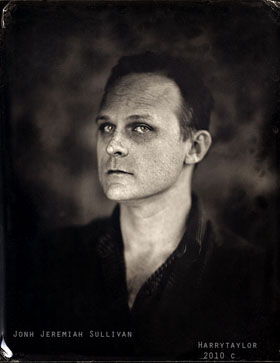 John Jeremiah Sullivan Wins Prize, Does Paris Review Proud by Lorin Stein
John Jeremiah Sullivan Wins Prize, Does Paris Review Proud by Lorin Stein
 A Big Week! by Thessaly La Force
A Big Week! by Thessaly La Force
 Schumer’s Warning
Schumer’s Warning
 Swole Jeff Bezos joins Instagram to tease his new ROCKET FACTORY
Swole Jeff Bezos joins Instagram to tease his new ROCKET FACTORY
 Nostalgia Act
Nostalgia Act
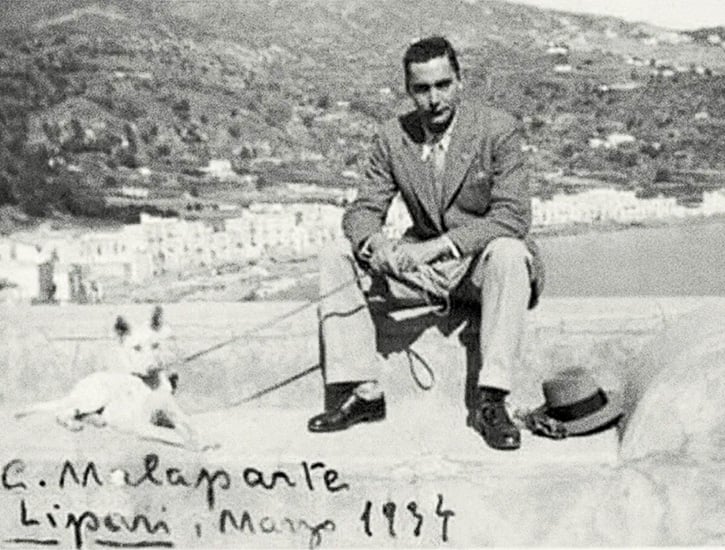
 Feminist Fascisms
Feminist Fascisms
 Best smartphone deal: Save $250 on Google Pixel 9
Best smartphone deal: Save $250 on Google Pixel 9
 Revenge of the Courtier
Revenge of the Courtier
 Miami Heat vs. Brooklyn Nets 2025 livestream: Watch NBA online
Miami Heat vs. Brooklyn Nets 2025 livestream: Watch NBA online
 Google launches citizen science project to help protect coral reefs
Google launches citizen science project to help protect coral reefs
 Perfecting the Art of Pedantry
Perfecting the Art of Pedantry
 Google launches citizen science project to help protect coral reefs
Google launches citizen science project to help protect coral reefs
 Best laptop deal: Get the 14
Best laptop deal: Get the 14
 A Ceasefire Is Not Enough
A Ceasefire Is Not Enough
How to support the fight for equal payI'm the leader of the White Walkers and here's why we're taking so longCarly Rae Jepsen's single anthems shine among her loveLinkedIn wants to pair you with someone special. No, not like that.Netflix's 'The Trial of the Chicago 7': Separating fact from fictionLiterally 47 minutes of Putin fishing, swimming, and generally living his best lifeChevy Bolt EV's back seat fires prompt federal investigationHow returnships can help during a femaleNokia wins NASA contract to put a 4G network on the moonHow returnships can help during a femaleYouTube bans ‘harmful’ QAnon, Pizzagate, and other conspiracy theory contentIn France, you still get EarPods with new iPhonesZoom launches new marketplace to charge for virtual eventsThere's a new kind of snowflake in town: the 'Broflake'Twitter goes down, and it's probably for the bestHere’s how Apple will make your iPhone 12 pickup coronavirusCool cat gives smoother high fives than most humansMac with new chips may launch at Apple event next monthSilicon Valley's gossip app is all over the place on the 'Google Manifesto'How black holes can spaghettify stars that fall too close The Immortality Chronicles, Part 4 by Adam Leith Gollner Drinking with Salinger by Sadie Stein Ancient Vintage, and Other News by Sadie Stein The Immortality Chronicles, Part 2 by Adam Leith Gollner Twitter returns to the old version of TweetDeck How to add custom emoji to Slack Don't spontaneously FaceTime people and expect them to pick up How to silence unknown callers on WhatsApp Reddit's API protest just made John Oliver a special job offer Past Tense by Sadie Stein Reader’s Block by Diane Mehta Wordle today: Here's the answer and hints for July 11 William Faulkner’s Unexpected Art, and Other News by Sadie Stein What We’re Loving: Taxidermy, Heroines, Bad Ideas by The Paris Review Tucker Carlson's Twitter show viewership is declining Secret Book Landscapes, and Other News by Sadie Stein Mr. Paradise by Jonathan Segura What We’re Loving: Wittgenstein, Hopper, Strangers by The Paris Review Letters from Jerry by Shelley Salamensky How to save disappearing messages on Whatsapp
1.6851s , 10137.5390625 kb
Copyright © 2025 Powered by 【Watch Flesh Clerk Who Shoves You Up And Down Online】,Wisdom Convergence Information Network